Our goal with TorBox is not only to simplify the use of Tor as an anonymizing router but also to bring the use of bridges closer to those who want to get around censorship easily — with all their network traffic, not just their browser traffic.
TorBox v.0.3.1 comes one step closer to this goal. Not only has the management of OBFS4 bridges been improved once again, but it’s also now possible to check the status of bridges (online, offline, or doesn’t exist anymore) and based on that to enable, disable and delete them. For operators of a bridge relay, the possibility to backup and restore the relay data has been implemented. Also, other smaller improvements and wishes have been taken into account, which are listed in detail below.
Since we also had to update the configuration files, we recommend using the new image rather than updating an existing system. We have added a short guide at the end of this post for those who absolutely must update from the previous version (not older!).
TorBox Image (about 675 MB): v.0.3.1 (30.05.2020) – SHA-256 values
TorBox Menu only: v.0.3.1 (30.05.2020) – SHA-256 values
We would appreciate feedback so that we can make further improvements. The three most valuable feedbacks will get a ProtonMail $100 Gift Card (sent as a PDF). Additionally, we have still one Raspberry Pi 3 Model B to give away — of course, installed with the latest TorBox version. If you are interested, just send us an email.
Changelog: v.0.3.0 (12.01.2020) –> v.0.3.1 (30.05.2020)
- Update: The system is based on Raspberry Pi OS “Buster” Lite with Linux Kernel 4.19.118 and Tor version 0.4.2.7.
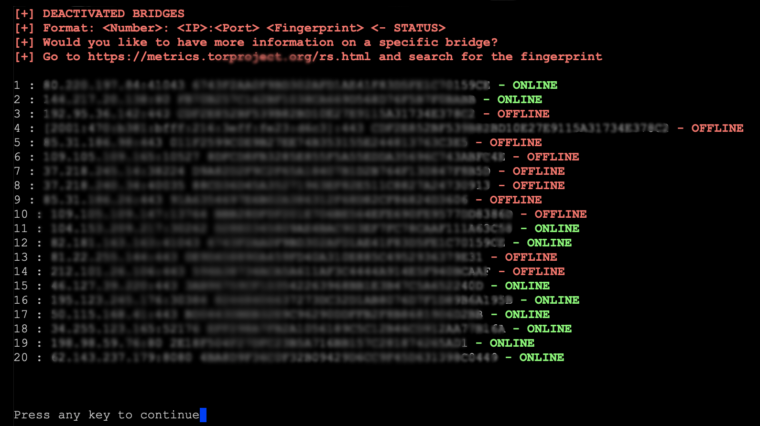
- New: The list of OBFS4 bridges displays now the status of the bridge (online, offline, or doesn’t exist anymore – see image below). The bridge management is rewritten. You can now easily activate, deactivate, and remove bridges in three ways: all, based on a specific status of the bridge or only selected. For example, you could activate all bridges, deactivate only the offline ones, and remove bridge #3 and #5.
- New: The ability to backup and restore your bridge relay configuration, including your identity keys. This is important because when upgrading your bridge relay or moving it on a different computer, the important part is to keep the same identity keys. Keeping backups of the identity keys so you can restore a relay in the future is the recommended way to ensure the reputation of the relay won’t be wasted. The backup is stored / can be placed in the home directory, in which you can download / upload it with an SFTP client (using the same login / password as the SSH client).
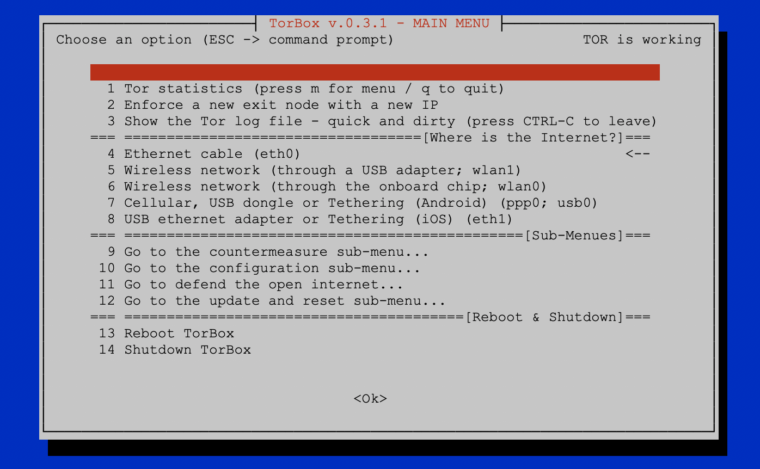
- New: An arrow in the main menu indicates from where you get the Internet.
- New: USB Tethering with Android devices should now work (main menu entry 7). As I do not have an Android test device, this point needs to be tested further, and I rely on your feedback. I want to thank everyone who has been in active email correspondence with me on this point over the past weeks.
- New: Added “Just fixing and cleaning” into TorBox’s Update & Reset sub-menu.
- Improved: The countermeasure against a disconnect when idle feature (entry 10 in the Countermeasure sub-menu)shows now its status and can be deactivated.
- Improved: Before Tor is compiled (option 3 in the Update & Reset sub-menu), the current version is checked, compared with the one in the repository, and the user can decide if he wants to aboard before wasting time if no new version is available. Important: Currently, Tor can be updated with option 1 “Update the base system” in the Update & Reset sub-menu (main menu entry 12), and it is not necessary to compile Tor fresh.
- Improved: The overall reliability of the update script.
- Improved: The overall reliability of the installation script. It is adapted to the new Raspberry Pi OS, and we hope that this is the beginning of a platform-independent use of TorBox .
- Improved: Cleaned up the code and outsourced more essential functions into a library. This helps to maintain the code in future releases properly.
- Fixed: After shutting down the Bridge Relay, the two ports remained open (at least in some instances).
- Fixed: If the Bridge Relay is deactivated and Tor is freshly started, the message appears that the ports are opened to the outside, even if this is not the case.
- Fixed: An error in changing the password of the Tor control port broke the enforcing of a new exit node with a new IP (main menu entry 2).
- Fixed (post-release): rfkill blocks the Raspberry Pi’s onboard WiFi chip and impossibles to create TorBox’s WiFi (it seems to be newly activated with Raspberry Pi OS) – we set rfkill unblock all in /etc/rc.local and had to rebuild the image again on Sunday, Mai 31, 2020 (we kept the same filenames).
How to update from TorBox v.0.3.0 (12.01.2020)?
Important: You cannot automatically update on TorBox installations, which are older then v.0.3.0 (12.01.2020)! If you need help, then please contact us.
With a TorBox v.0.3.0 (12.01.2020) installation, you can perform the following tasks. This deletes all your custom made configuration, but not alter your bridge relay keys. Nevertheless, we recommend, if possible, to use the new image.
- Go to the Update & Reset sub-menu (main menu entry 12).
- Select options 1, 4 and 6
- Restart TorBox
Your feedback is welcome!!
We hope this version pleases you. However, we are dependent on feedback. It’s not just about fixing bugs and improving usability, but also about supporting additional interfaces and hardware in future releases:
- What do you like?
- What should be improved (and how)?
- What would you like to see next? Which features do you request?