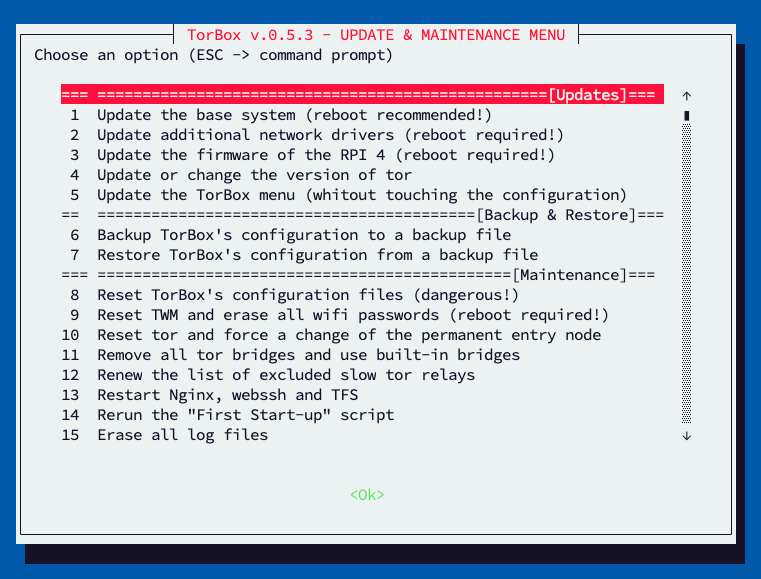
The primary purpose of this sub-menu is to backup and restore TorBox ‘s configuration (including OBFS4 Bridge Relay and Onion Service), update or even reset your TorBox, and fix some inconveniences, if necessary. In the following, we look at all menu entries one by one:
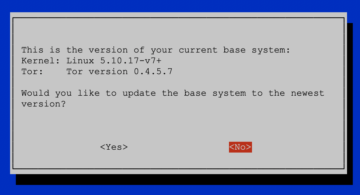
- Menu entry 1: Update the base system: This menu entry updates your base system, including the Linux kernel. Before the update starts, the current version of the installed Linux kernel and Tor is displayed. The update begins after another confirmation and can last up to 30 minutes. It runs in a screen session, meaning that if you close the SSH client or lose the connection to the TorBox, the update process continues until all is done. You can always make a new SSH connection, leave the menu with ESC and execute
screen -xto see the update’s progress. Do not remove power from your TorBox during the update. A reboot is highly recommended after an update and is necessary to load a new kernel.
Important
.- Updating the Linux kernel may mean that the additional network drivers are not supported anymore.
- You must run entry 2 to update the additional network drivers in this case.
- Updating the base system may also install an older version of Tor. In this case, please rerun entry 4.
- However, updating the base system doesn’t update the TorBox menu, but you can use entry 5.
- Menu entry 2: Update additional network drivers: This menu entry updates the additional installed network drivers (Realtek 8188eu, 8188fu, 8192eu, 8812au, 88x2bu, 8814au, 8821au, and 8821cu). This should simplify the use of 5 GHz band wifi USB adapters.
- Menu entry 3: Update the firmware of a Raspberry Pi 4 or 5: Does what it says! It is only supported by a Raspberry Pi 4 or a Raspberry Pi 5. If something goes wrong, your EEPROM could be left corrupted, and the RPI4/5 won’t boot again. In such a case, download and use the Raspberry Pi Imager to create a Recovery SD Card. For more information, see here.
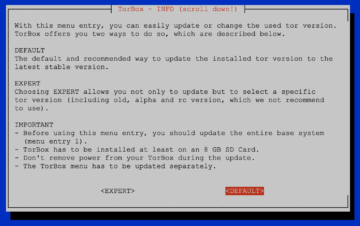
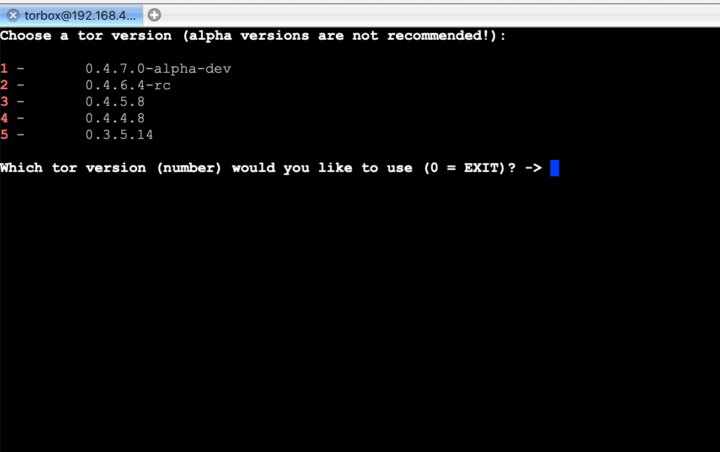
- Menu entry 4: Update or change the version of tor: This menu entry updates or changes the installed tor version. It can be chosen between “DEFAULT” and “EXPERT”, where “DEFAULT” installs the latest stable tor version and “EXPERT” gives access to a variety of tor versions, including the -rc and -alpha versions (which is not recommended to use).
The update runs in a screen session, meaning that if you close the SSH client or lose your connection to the TorBox, the update process continues until all is done. You can always make a new SSH connection, leave the menu with ESC and executescreen -xto see the update’s progress.
Important
In the “DEFAULT” mode, the current version of the installed Linux kernel and Tor is displayed before the update starts, which is the case after another confirmation. The update procedure can last up to 30 minutes. Do not remove power from your TorBox during the update.
- Menu entry 5: Update the TorBox menu: This menu entry fetches and installs the latest stable version of the TorBox menu from its GitHub repository. However, this menu entry will not update / overwrite / reset TorBox’s configuration files — usually, this is not necessary for minor updates. Check our blog entries for major updates, and update / change TorBox’s configuration files if necessary.
Choosing “DEFAULT” will install the newest TorBox menu from the master branch of TorBox’s GitHub repository. “EXPERT” let you install the TorBox menu from another fork or branch.
- Menu entry 6: Backup TorBox’s configuration to a backup file: This entry makes a backup of your entire TorBox configuration, including the general configuration, the bridge relay configuration, and the Onion Services, optionally with all shared folders. The backup file will be stored in
/home/torbox/backup. You can access the backup file by downloading it from your TorBox using a SFTP client (it uses the same login and password as your SSH client). Alternatively, you can retrieve the backup file by connecting an USB stick to your TorBox. You may mount the USB stick withsudo mount /dev/sda /mntand then copy the backup file on your stick.
With this backup, upgrading a TorBox with a bridge relay or Onion Services, as well as moving the configuration to another computer keeping all the configuration, keys, Onion domain name, and data, is possible. Regarding bridge relays, keeping backups of the identity keys to restore a relay in the future is the recommended way to ensure the reputation of the relay won’t be wasted. Also, backups of the Onion Services is the recommended way to ensure the availability of your data in case of a system crash.
Important
.- An already existing backup-file in the home directory will be overwritten without confirmation!
- If you choose to make a backup of your shared folders, you need enough space on your SD card.
- Menu entry 7: Restore TorBox’s configuration from a backup file: This entry restores a backup, including the general configuration, the bridge relay configuration, the Onion Services, and the shared folders. The restored backup file must be located in the TorBox home directory (
/home/torbox). You can upload a backup file using an SFTP client (it uses the same login and password as your SSH client). Alternatively, you can transfer a backup file by connecting a USB stick to your TorBox. You may mount the USB stick with sudo mount/dev/sda /mntand then copy the backup file from the stick to your home directory.
Important: Only a backup made with menu entry 6 can be restored! Already existing configurations will be overwritten without confirmation!
- Menu entry 8: Reset TorBox’s configuration files: This menu entry copies the original configuration files from ~/torbox/etc to the right places on the system.
Important
All configuration files will be overwritten, and all your custom configurations will be lost!!
- Menu entry 9: Reset TWM and erase all wifi passwords: Does what it says!
- Menu entry 10: Reset Tor and force a change of the permanent entry node: Sometimes, especially if you did not use TorBox for a longer time, Tor gets stuck during its boot process (for example, at “Bootstrapped 0%”). This menu entry resets Tor so that it functions normally again. Additionally, this menu entry enforces a change of the entry guard, which could be necessary if the entry guard becomes unstable (this will be mentioned in the log file). Notice that enforcing a new exit node (main menu entry 2) does not change the entry guard, which usually remains for 2-3 months to protect against a known anonymity-breaking attack (for more information, see here).
- Menu entry 11: Remove all tor bridges and use built-in bridges: This entry removes all tor bridges, fetch and use built-in bridges from the TorBrowser. It this is a measure of last resort if nothing else gives you workable bridges.
- Menu entry 12: Renew the list of excluded slow tor relays: In the Configuration sub-menu, the exclusion of tor relays which are slower than the given speed threshold can be activated. This list is static and should be renewed from time to time. That’s what this menu entry does.
- Menu entry 13: Restart Nginx, webssh and TFS: Does what it says!
- Menu entry 14: Rerun the “First Start-up” script: Does what it says! (Check out the related documentation)
- Menu entry 15: Erase all log files: Does what it says!
- Menu entry 16: Time synchronisation: Does what it says!
- Menu entry 17: Just fixing and cleaning: This menu entry fixes and cleans the installed packages. It also removes dependencies, which are not anymore necessary. Running this menu entry also fixes OBFS4 attributions and the tor service files.
• • •
Problems and questions
- The TorBox Wireless Manager seems to crash instead of showing me wireless networks! What’s wrong here? –> see here.
- Tor did work without a problem. The Internet is reachable. Nevertheless, after a restart of TorBox, Tor does not load anymore. It has been stuck at “Bootstrapped 0%” for more than 5 minutes! How can I fix that? –> see here.
- Why is the local TorBox traffic not routed through tor? Why is by default Google’s and/or Cloudflare’s service used to circumvent cheap censorship measures or to test the connectivity? Can I change Google and/or Cloudflare services with something else? –> see here.