With the current release, we were focused on improving the functionalities in TorBox. For example, TorBox Chat Secure can now be a chatroom with an “open” channel for all participants and private channels (similar to the old and mighty IRC). We also added support and generation of SSH keys for the TorBox login, even though we stuck to the password authentication as default. However, turning off the password authentication in favor of the SSH public key authentication is possible and added to the Danger Zone sub-menu. The Danger Zone sub-menu comprises more risky features or ones still in testing. For example, you will find in this sub-menu a feature to exclude domains from tor protection. In other words, starting with this version of TorBox, you can decide that certain domains are always directly connected. This feature was a request from a user who wanted specific governmental sites in an authoritarian country to be connected directly and not through tor, even if he used tor for all other connections to protect himself. This feature can be helpful but is highly dependent on your threat model. If not applied in the right way, this feature can be harmful. We will add more features in this sub-menu with the next release. Aside from these new or improved features, we fixed a lot under the hood, which should improve usability. To do so in the future, we need your feedback. With the TorBox GitHub repository, it is straightforward for everyone to report issues or change the code and propose it in a pull request.
TorBox Image (about 1.1 GB): v.0.5.3 (09.07.2023) – SHA-256 values
TorBox Menu only: v.0.5.3 (09.07.2023) – SHA-256 values
Since we had to install additional software packages and update the configuration files, it is necessary to use the new image or reinstall TorBox using one of our installation scripts.
• • •
Changelog: v.0.5.2 –> v.0.5.3 (09.07.2023)
- Update: The system is based on Raspberry Pi OS “Bullseye” lite (64-bit) with Linux Kernel 6.1.21 and Tor version 0.4.7.13 with obfs4proxy version 0.0.14 and Snowflake 2.6.0. All installation scripts are updated to work with Raspberry Pi OS “Bullseye” (64-bit), Debian 11, 12, Ubuntu Server 22.04.02 LTS, and Ubuntu Server 23.04. We also improved the compatibility with Debian and Ubuntu and updated TorBox’s internal list of OBFS4 and Snowflake bridges.
- Update: Realtek RTL8821CU wireless network driver
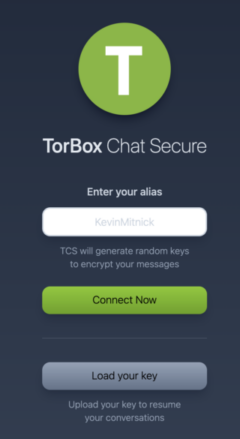
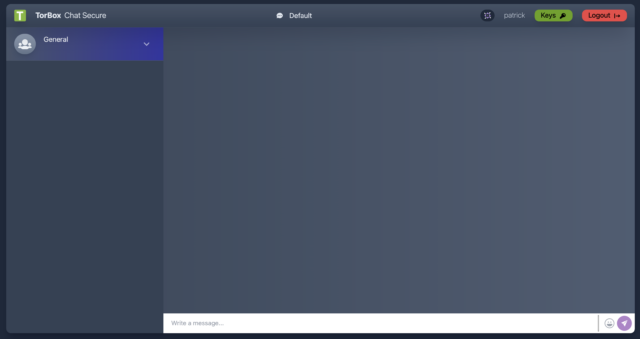
- Update: TorBox Chat Secure version 2.0 (TCS). The idea behind the new version is to have a chatroom rather than only a person-to-person messenger. Also, by downloading a key, people can leave the chat room and log in later to see the “open” conversations and their messages in the private channels. All conversations are encrypted on the TorBox, but cannot be decrypted without the key. Turning TCS off will delete all encrypted data.
- New: The Danger Zone sub-menu collects features that are considered risky or could compromise the user’s security and anonymity. Therefore these features should only be used if the user knows the potential risks and consequences. For example, the “forwarding only” mode for client data traffic will function as a router without tor protection. This feature was also a request, but most of the time, it makes only sense in connection with developing and debugging.
- New: Also, in the Danger Zone sub-menu, we added the possibility of excluding domains from being routed through tor. TorBox will communicate directly with the destination without protection if the domain is on the exclusion list. For example, if you use TorBox in the country Authoritarian (.aaa), you may use tor for all communications, but not when you have to go to a governmental website (let’s say
www.government.aaa). In this case, you can excludegovernment.aaafrom being routed through tor. Another use case could be that you want to stream something that doesn’t need protection (for example, a local music station) but uses much bandwidth. Please remember that tor does not protect the traffic to/from the IPs on the exclusion list. It would be best to assume that everyone will see that you connect these IP addresses. If not correctly encrypted (for example, by using HTTP, which is blocked by default), everyone can see the content of the communication to/from these IP addresses! - New: During the start-up of TorBox, by default, there is a failsafe in place to put TorBox’s AP back on
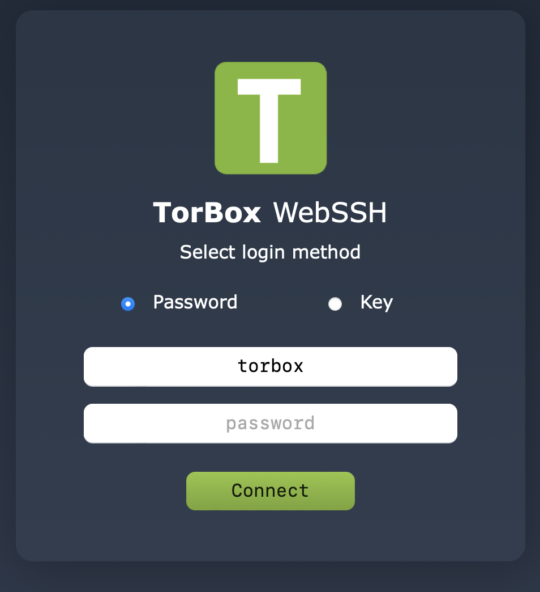
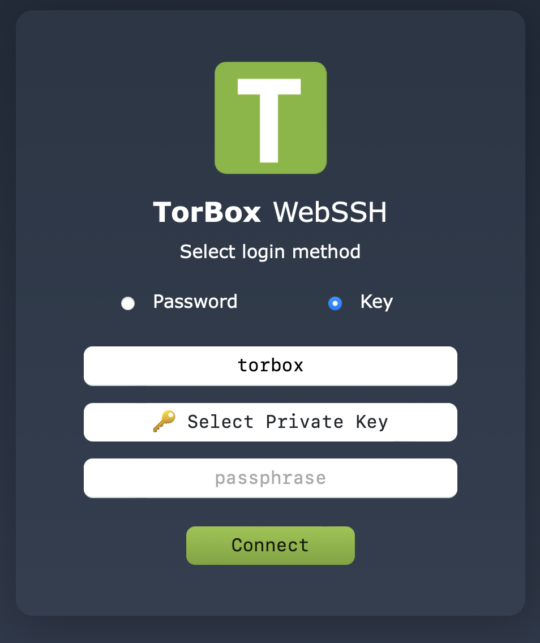
wlan0if it was used on wlan1. It will prevent a lock-out of the TorBox user. Based on another user request in the Danger Zone sub-menu TorBox’s AP can be permanently put on wlan1. - New: In the configuration sub menu, we added support and generation of SSH keys for the TorBox login. If SSH public key authentication are configured, it is possible to turn off SSH password login in the Danger zone.
- New: WebSSH supports now SSH keys. Also, we applied the new style from TCS to WebSSH.
- New: In highly authoritarian countries connecting the tor network could be seen as suspicious. Because ISPs can see, log, and even block hostnames, the installation scripts and also the first start-up dialogue allow changing or randomizing the default hostname of the TorBox. There is also a new entry in the countermeasure sub-menu, which allows to change or randomize a hostname later. This feature was also based on user feedback.
- New: You can remove all tor bridges , fetch and use built-in bridges from the TorBrowser in the Update and Maintenance sub-menu. However, we think this is only a measure of last resort if nothing else gives you workable bridges.
- New: The Update and Maintenance sub-menu gives the possibility to synchronize TorBox’s time via ntp. If this fails, the user will be prompted to enter the right time and date.
- New: In the last TorBox version we added the possibility to exclude of slow relays. In this version we added the possibility to renew the exclusion list Update and Maintenance sub-menu.
- New: Insecure http requests are blocked by default. However, currently, there is no way to overcome the shortcomings of this kind of blocking. It will not work for applications and clients using TorBox’s SOCKS 5 functionality, in a VPN over Tor or a Tor over Tor situation.
- New: Using “AvoidDiskWrites 1” in
torrc, which will lead to tor writing less frequently to disk than we would otherwise. - Fixed: Snowflake and Meek functionality (they need local DNS resolution, which was still blocked).
- Fixed: The OFFLINE/ONLINE status of Snowflake- and Meek-Bridges is always labeled as OFFLINE in the bridge database. Therefore, the status is no longer taken into account and is removed.
- Fixed: VPN support.
- Fixed: Sometimes, pressing the ESC key didn’t close the menu, instead, it reloaded again.
- Fixed: The WLAN regulatory domain was not set permanently.
- Fixed:
rc.localwill now work more reliably and automatically establish a tor connection if possible and previously used. - Improved: VPN over WLAN starts the Torbox Wireless Manager (TWM) if the connection with
wlan0is not established. It also supports captive portals deployed from WLAN. However, there is no need for captive portal support before connecting with the VPN provider (that was an error). Unfortunately, we couldn’t test all VPN-client/Internet interface combinations yet and need more feedback. - Improved: If TorBox could not synchronize the system time during booting, tor would not load. The first start-up dialogue covers that, and if an automatic synchronization isn’t possible, the user will be asked for the correct date and time.
- Improved: Installing TorBox on unreliable bandwidth connections could be problematic. The install scripts have new added some tests to check if the necessary packages are installed. If packages are missing, the connection is rechecked and a new attempt to install the package is made. In some cases (for example go, tor, …), if the download of a package is not possible, the installation script try other ways to install it.
- Improved: Implementation of a new, more reliable way to install, update and check Python modules.
- Improved: The usability of reactivating Onion Services.
- Improved: TWM will work now with special characters. Also, is TWM confronted by WPS, it will not ask for a password.
- Improved: If the Bridge Relay is configured for the first time, but tor is not restarted, the user will be reminded to restart tor when looking up his personal OBFS4 bridge address.
- Improved: Resetting tor in the Update and Maintenance sub-menu will also deactivate the exclusion of slow tor relays.
- Improved:
rfkillis now soft-blocking bluetooth. - Improved: Installs/updates automatically the newest version of go.
- Improved: Compatibility for Debian and Ubuntu.
- Improved: We’ve cleaned up the project’s file structure and tucked all the helper scripts into the
bindirectory. - Security: Path traversal vulnerability in TFS fixed (see here: https://www.acunetix.com/vulnerabilities/web/path-traversal-via-misconfigured-nginx-alias/)
• • •
How to update from TorBox v.0.5.2?
Again: Since we had to make substantial changes in the configuration files, it is recommended to use the new image or reinstall TorBox using one of our installation scripts. Nevertheless, you can perform the following tasks to update a TorBox v.0.5.2 installation. It will delete all your custom-made configurations.
- Please, make sure that TorBox has Internet connectivity.
- Go to the Update and Reset sub-menu, update the TorBox menu and reset TorBox’s configuration files (entries 1 and 6).
- Manually compare if
torrcin/etc/tor/torrc(compare with the GitHub version) and the runfile (run/torbox.run-> compare with the GitHub version) have similar entries. If unsure, just copy the versions from the GitHub repository over the ones on your system (/etc/tor/torrcand/home/torbox/torbox/run/torbox.run). - Reboot TorBox, and again, make sure that TorBox has Internet connectivity.
- Go to the Update and Reset sub-menu, and update the base system (entries 1).
- Manually install
ipsetandrfkill(only for Debian and Ubuntu). - Reboot TorBox, and again, make sure that TorBox has Internet connectivity.
- Update the rest in the Update and Reset sub-menu: additional network drivers with entry 2, and tor with entry 4
- Reboot TorBox.
• • •
We need your feedback!!
We hope this version pleases you. However, we are dependent on feedback. It is not just about fixing bugs and improving usability, but also about supporting additional interfaces and hardware in future releases:
- What do you like?
- What should be improved (why and how)?
- What would you like to see next? Which features do you request?
With the TorBox GitHub repository, it is straightforward for everyone to report issues or change the code and propose it in a pull request. Because we continue to travel around, it sometimes needs more time to address the issues and proposals.
For future versions, it is essential that we know what you need and want to see from the Onion Services implementation. Please feel free to use the discussion forum to tell us your needs.
• • •
Known problems and bugs
BUG: Because of a wrong path, the information windows after choosing “Restore TorBox’s configuration from a backup file” in the Update and Maintenance sub-menu is blank. You can fix the bug by updating the TorBox menu (update and maintenance sub menu entry 5) and and reselecting entry 7. BUG FIXED✔︎