I’m pleased to announce the release of TorBox v.0.2.4. As promised, the focus of this release was on supporting OBFS4 bridges, which help to overcome censorship measures in certain countries (for example Turkey). Below are the links for the latest TorBox v.0.24 (typically, you need only the image-file):
Changelog v.0.2.3 (09.02.2019) —> v.0.2.4 (25.05.2019)
Updated: The system is based on Raspbian “Stretch” lite with Linux Kernel 4.19.2 and Tor version 0.3.5.8.
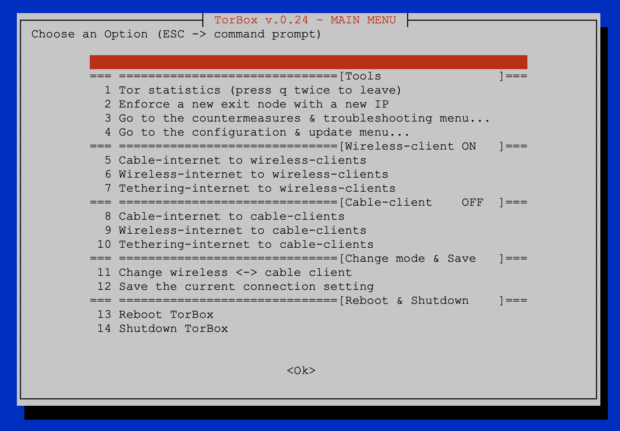
New: Instead of the “advanced submenu”, we split old and new functionalities into two separate submenus: “countermeasures & troubleshooting” and “configuration & update”.
New: We implemented in the “countermeasures & troubleshooting” submenu a user-friendly way to activate, configure, and change the OBFS4 bridge’s functionality. There are 15 pre-configured OBFS4 bridges in the configuration, which were fully functional at the time of the release. We hope to help with this approach beginners. We urgently need your feedback to develop this functionality further.
New: Since TorBox v.0.2.3, nyx does a good job as a statistics tool (main menu entry 1). However, there are certain cases, when Tor hangs during bootstrap, that nyx doesn’t start either. Therefore we have added an alternative method in the submenu “countermeasures & troubleshooting” (entry 11) to quickly display the log file of Tor and update the display if necessary.
New: TorBox is now providing a SOCKS v5 proxy functionality on port 9050 to its connected clients. If you use that capability, applications which support SOCKS v5 proxy connectivity and “DNS over proxy” (for example Firefox or the add-on FoxyProxy) can access directly .onion sites. For more information, see here.
Improved: We again reduced the size of the image file, which is now about 865 Mbyte.
Changed: All scripts are now executed by bash instead of sh. The change was needed to enable the handling with arrays.
Fixed: Some minor bugs and cleaned up the code.
Removed: The experimental section (for now).
The pre-v.0.2.5 release is expected at the end of the year.

Hello when i change the admin pi do i have to change the password or leave it as pi and change it
I recommend to leave the admin (root) to pi and only to change the password of it (see “Question 01” in the FAQ). The procedure is a little more complicated if you wish to change the admin name as well. Here you can find a tutorial on how to accomplish that (however, I didn’t test it out, yet). If the possibility to change the admin name is a wish, I could try to include it in the menu in the next upcoming version.
Hello,
How can I change the Tor port ?
Thanks
Hello Jack
In /etc/tor/torrc change one or several of these lines:
TransPort 192.168.42.1:9040
DNSPort 192.168.42.1:9053
SocksPort 192.168.42.1:9050
ControlPort 9051
Corresponding, you have also to change following lines in the script “set_interfaces”:
$IPTABLES -t nat -A PREROUTING -i $I_DEVICE -p tcp -j REDIRECT –to-ports 9040
$IPTABLES -t nat -A PREROUTING -i $I_DEVICE -p udp –dport 53 -j REDIRECT –to-ports 9053
$IPTABLES -t nat -A PREROUTING -i $I_DEVICE -p udp -j REDIRECT –to-ports 9040
…and in the script “new_ident”:
PORT=9051
LOCALPORT=9051
Could you give me the reason, why you want to change the Tor port(s)?
Thank’s a lot !
It’s because my routeur block the port 9051
That shouldn’t matter at all. Port 9051 is the control port, used locally. Also, the other above mentioned ports are only locally used. With other words, you connect TorBox via port 80 and iptables redirects it locally to port 9040.
Probably your router blocks the outgoing ports so that TorBox can’t reach the Tor network. In this case try to add “FascistFirewall 1” in /etc/tor/torrc without editing the script files (see also: https://2019.www.torproject.org/docs/faq.html.en#FirewallPorts).